iPhone, iPad and iPod touch users have many ways of keeping their data within reach and accessible. Most commonly, users copy and save data and information from their devices by creating a backup. This is typically performed when transferring current data to a new device. Since October 2011, Apple has enabled users with an internet connection to create a backup of their device using Apple’s iCloud. iCloud backups include nearly all data and settings stored on a device, such as contacts, notes, voicemail, photographs, videos and text messages and because a large portion of that data is stored in a database on the device to begin with, certain deleted information may be available within those backups as well. The backups do not include Mail or Health data [1]. Users can also backup Apple device data using iTunes. The process is similar to creating an iCloud backup, but users can also encrypt the iTunes backups to a personal or business computer (see below). With iTunes backups, the computer’s iTunes encryption password is necessary before the backup can be accessed and used.
As individuals and companies seek to secure data and protect data privacy, the role of encryption in this process and its impact is drawing greater examination and scrutiny, particularly from law enforcement. Data on an Apple device is encrypted so that no one but the user can access it. When that data is backed up to iCloud, it’s encrypted, but the user and Apple are able to access it. It was recently reported that more than two years ago, Apple dropped plans that would enable users to fully encrypt their backups in iCloud, which would have meant that no one other than the user would be able to access their data. Under the proposed program, “Apple would no longer have a key to unlock the encrypted data, meaning it would not be able to turn material over to authorities in a readable form even under court order. [2]” The program was primarily designed to thwart hackers. The project was reportedly dropped because Apple did not want to be exposed to attacks and claims by public officials and law enforcement that Apple was safeguarding information belonging to criminals and moving formerly available data out of reach of government agencies, law enforcement and the courts. Another reason the plan was discarded was the real concern that customers would forget their iCloud password and find themselves locked out of their data.
The FBI and other law enforcement agencies have routinely criticized Apple’s encryption of device data because it stands in the way of critical investigations. The proposed full encryption of iCloud backups raised the same concerns and would have rendered previously accessible data out of reach.
Nowadays, when the FBI has an iPhone in custody, they often rely on hacking software that exploits security flaws to break into a locked iPhone. For example, in the San Bernardino case, the FBI used a third-party company to break into the shooter’s iPhone – this can be very time and resource consuming. On the other hand, Apple’s iCloud can be examined in secret without alerting the user. According to Apple, it has turned over at least some data for 90% of the requests received from government agencies when subpoenaed, providing either full device backups or other content from the iCloud.
Apple has now moved its focus to protecting users’ sensitive information such as health data and saved passwords. Contact information and text messages from iMessage and WhatsApp that have been backed up remain accessible to Apple employees and authorities. Since abandoning their plan, which would have caused them to lose access to iCloud backups, Apple has shown significant willingness to cooperate with U.S. intelligence agencies and law enforcement, notwithstanding the high-profile cases that receive significant media attention.
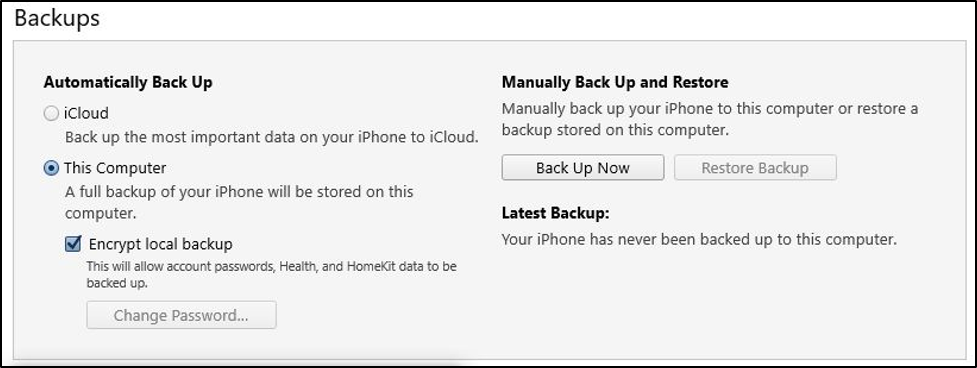
bit-x-bit regularly encounters iTunes encryption when preparing forensic extractions of iPhones and iPads. Frequently when an iPhone user configures their device with iTunes, they select to encrypt their backup locally which forces them to set an encryption password. Occasionally the user has not retained the encryption password, so they are unable to decrypt their iTunes backup. In these cases, the iTunes encryption password has to be reset, or we must reset settings on the device to remove the encryption password, therefore allowing us to prepare a decrypted backup. Not surprisingly, this process takes more time, and can substantially delay the recovery of critical information in the case or investigation.
To avoid these problems, we recommend that Apple users who choose to enable encrypted iTunes backups use a password manager, such as Dashlane or LastPass, to store that password. Many people either use weak passwords or reuse passwords for multiple accounts, which makes them more vulnerable to crimes, such as identity theft. A password manager will generate, retrieve and keep track of passwords while also protecting vital online information. This does not only involve passwords, but PINs, answers to security questions and more. Password managers have robust encryption and when combined with a strong password it should take a hacker decades to break. For all this security, you only need to remember a single password. For most users, this offers a much better combination of security and convenience than not using a password manager. The key thing to remember – keep your master password secure. Most password managers do not let you reset your password if you are locked out.